Should you care about CyberCrime?

“I don’t really get computers…” This is one of the most common comments we receive from our happy customers at some point during our services. Computers and their technical jargon are, for many people, overwhelming and unimportant. Terms like “antivirus” and “firewall” are often only loosely understood. When it comes to “cybercrime”, a lot of people aren’t really sure what exactly cybercrime is, or what it means to them. Read on to learn about cybercrime, cybersecurity, and why you should care.
What is CyberCrime? Why should you care?
Cybercrime is simply any criminal activity carried out by use of computers and the Internet. Cybercriminals are automating the extraction of data and assets from individuals and businesses by harnessing the power of modern technology and the Internet. In 2016, cybercrime was the second most reported crime globally. It is predicted that by 2021, the global damage cost of cybercrime will be $6 trillion USD.
Fortunately, you can minimize the risk to yourself, your family, or your place of work by taking only a few minutes to learn some basic terminology.
It is very common to mentally “switch-off” when we see technical words and jargon we are not familiar with, but take a quick look at this helpful infographic from the UK’s National Cyber Security Centre (NCSC) – you’re sure to learn something that will help to protect you and your data online.
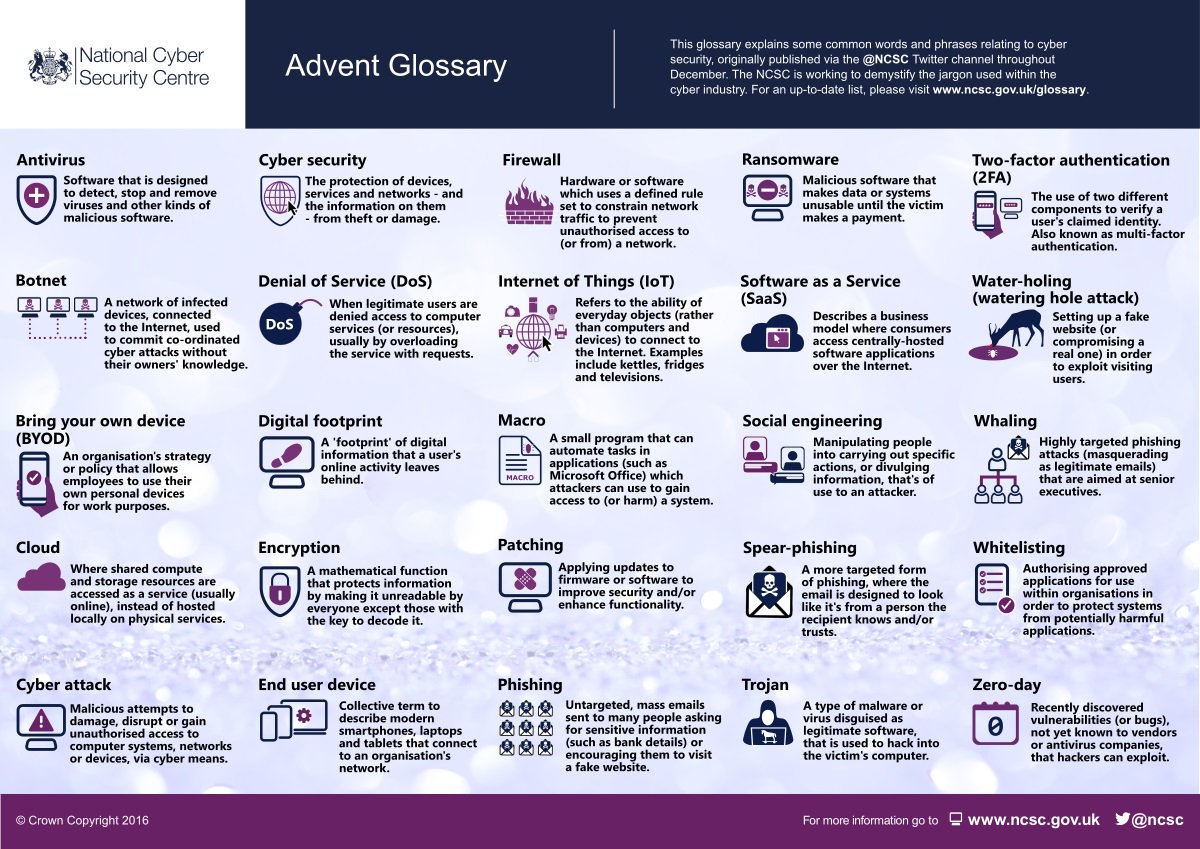
We recommend that you familiarise yourself with the following concepts in particular from the image as a good base for your own information security or #InfoSec.
#Antivirus
Imagine that your PC is like your home. Your AV or Antivirus works much like a combination of security cameras, guard, and a patrol dog. All constantly watching, searching, and sniffing out any intruders, and stopping and detaining any that are found.
#Firewall
If your AV is your security patrol, your #Firewall is like building bigger walls, installing improved door and window locks, and adding a perimeter fence which only allows safe items in and out.
#Ransomware
Imagine someone managed to enter your home and take physical control of your property – making it completely unavailable to you until you meet their demands – usually paying a significant amount of real money.
Ransomware is essentially the digital version of this: your files or whole PC are made completely unusable and inaccessible (using complex mathematical encoding known as encryption) until you pay the “ransom” to regain access.
Ransomware has rapidly come front and centre in terms of cybersecurity – look out for an upcoming Ransomware special focus blog post!
#Phishing
Phishing is a little like mass-mailing leaflets to a whole town of homes – it’s a numbers game, with criminals hoping that someone – anyone – will bite. Attackers are hoping that they have correctly guessed a service which you actually use.
Using email, attackers impersonate legitimate people or businesses in an attempt to trick you into providing them, a FAKE company, with REAL information for your REAL account. The goal is, of course, to profit from you in some way.
#SpearPhishing
While Phishing is a wide-spread approach; Spear-Phishing is much more targeted. Criminals have already identified a specific company or individual which you do actually have an existing relationship with, as opposed to guessing as with “Phishing”.
The email will be designed to look identical to one from someone you know or trust, but the goal is the same – to steal your information for profit.
#Trojan
Just like the concept of the Trojan horse, Trojan software is designed to look like a legitimate piece of software, and often it will even perform legitimate functions. However, the true purpose is to gain access to your PC, either to steal your data, or to use your PC as part of a Botnet.
#Botnet
If your PC is infected with a virus, Trojan, or other malware; it could become part of a Botnet.
A Botnet is simply a number of virus-infected PCs or other devices, connected to the internet, and used in unison to commit larger cyber-attacks without the knowledge of the device owners. In this way, #CyberCriminals can hide behind an “army” of PCs and locations, and use the computing power of other peoples PCs to commit crimes.
Please get in touch with AnyTech365 if you have any concerns about #CyberCrime or #Hackers, or even if you just have an annoying little pop-up, or if your PC or any of your IoT (Internet of Things) devices seems slow: we’re here and ready to help you – in 13 languages!
IoT Security Solutions from friendly IT experts | AnyTech365

